- White Glove Managed IT
- Simulated Scenario Testing
- Remote Desktop Server
- Remote Access Configuration
- Virtualization Setup & Maintenance
- Virtual Server Hosting
- Tech365 Cloud Support
- Amazon AWS & Google Cloud
- Tech365 Managed Backup
- Google Apps & Office 365
- Amazon AWS & Google Cloud
- Managed Enterprise DNS
- Tech365 Website Hosting
- Tech365 Hosted Business Phone
- Tech365 Network Monitoring
- Tech365 Managed Backup
- Virus and Spyware Removal
- Virtualization Setup & Maintenance
- Complete Systems Backup
- Disaster Recovery
- Microsoft Azure Setup & Management
- Monday.com Setup, Integration, & Automation
- Periodic Recovery Testing
- Simulated Scenario Testing
- Redundant Backup Infrastructure
- Tech IT Out
- About
- Services
- White Glove Managed IT
- Onsite & Physical IT Support
- Remote, Cloud, & Helpdesk Support
- Simulated Scenario Testing
- Remote Desktop Server
- Remote Access Configuration
- Virtualization Setup & Maintenance
- Virtual Server Hosting
- Tech365 Cloud Support
- Amazon AWS & Google Cloud
- Tech365 Managed Backup
- Google Apps & Office 365
- Amazon AWS & Google Cloud
- Managed Enterprise DNS
- Tech365 Website Hosting
- Tech365 Hosted Business Phone
- Compliance Services
- Business Continuity
- Tech365 Network Monitoring
- Tech365 Managed Backup
- Virus and Spyware Removal
- Virtualization Setup & Maintenance
- Complete Systems Backup
- Disaster Recovery
- Microsoft Azure Setup & Management
- Monday.com Setup, Integration, & Automation
- Periodic Recovery Testing
- Simulated Scenario Testing
- Redundant Backup Infrastructure
- Security Services
- Custom App Development
- Website & Internet Marketing
- Industries
- Tech IT Out
- Let’s Connect
- About
- Services
- White Glove Managed IT
- Onsite & Physical IT Support
- Remote, Cloud, & Helpdesk Support
- Simulated Scenario Testing
- Remote Desktop Server
- Remote Access Configuration
- Virtualization Setup & Maintenance
- Virtual Server Hosting
- Tech365 Cloud Support
- Amazon AWS & Google Cloud
- Tech365 Managed Backup
- Google Apps & Office 365
- Amazon AWS & Google Cloud
- Managed Enterprise DNS
- Tech365 Website Hosting
- Tech365 Hosted Business Phone
- Compliance Services
- Business Continuity
- Tech365 Network Monitoring
- Tech365 Managed Backup
- Virus and Spyware Removal
- Virtualization Setup & Maintenance
- Complete Systems Backup
- Disaster Recovery
- Microsoft Azure Setup & Management
- Monday.com Setup, Integration, & Automation
- Periodic Recovery Testing
- Simulated Scenario Testing
- Redundant Backup Infrastructure
- Security Services
- Custom App Development
- Website & Internet Marketing
- Industries
- Tech IT Out
- Let’s Connect
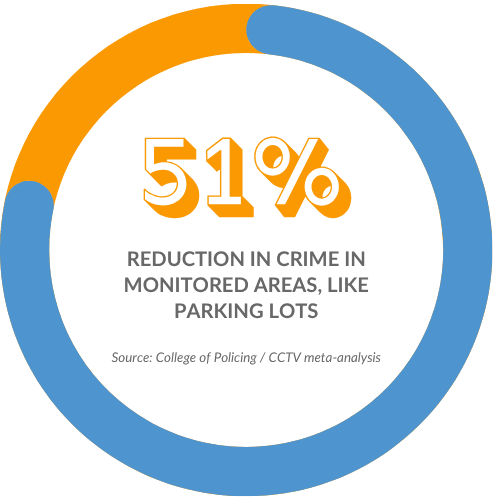
Camera & Security Installations For Businesses
Get full visibility and control over your business with professionally designed camera and access control systems.
LET'S CONNECT
Have a question or need help? Drop us a note below and we'll be in touch soon.
"*" indicates required fields
Security Systems That Protect Your Business
Cameras, access control, and security systems work best when they’re set up correctly and managed as one system. The goal is simple: make it easier to monitor your business, control access, and respond when something happens.
ACCESS CONTROL & ENTRY
LET'S START WITH A COMPLIMENTARY IT CONSULTATION
Let’s review your cameras, access control, and setup to see what makes the most sense for your business.
Camera & Security Installation for Any Size Setup
We monitor your systems continuously to detect unusual activity and stop threats before they impact your business. By identifying problems early, we reduce disruptions and keep your operations running smoothly.
Cameras & Surveillance
Access Control & Security
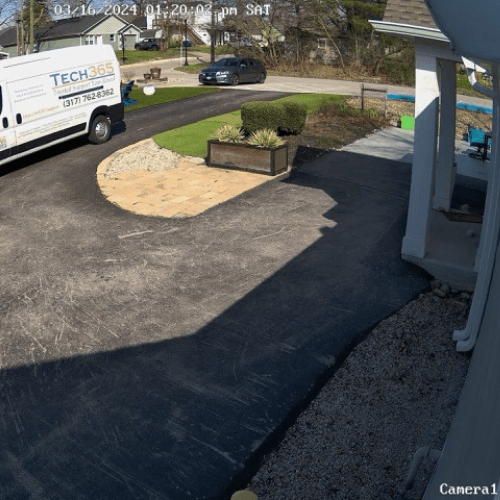
Camera System Design & Coverage
Your camera system should cover every part of your business, not just a few key spots. We design placement to eliminate blind areas and give you clear visibility where it matters most.

Entry Points Covered
Cameras placed to clearly capture who is coming and going, including visitors, staff, and deliveries.
Interior Coverage
Coverage focused on key areas like hallways, shared spaces, and main work zones without over-monitoring.
Exterior & Perimeter
Visibility across parking areas, building edges, and entry paths, especially for after-hours activity.
Special Areas
Custom placement for spaces like warehouses or multi-room layouts where standard setups don’t work.
Access Control Without The Guesswork
Managing who can access your building shouldn’t rely on keys, shared codes, or memory. We set up systems that give you full control over entry, access levels, and activity across your business.
Control Who Gets In
Remove Access Instantly
Track Entry Activity
Work Across Your Locations

Where Security Breaks Down
Without the right systems in place, it’s difficult to see what’s happening or control who has access. These gaps create risks that show up in day-to-day operations.
When systems aren’t in place or aren’t set up correctly, these are the problems that show up:
Camera and Security Installations in Real Environments
Each setup is based on the layout, access points, and needs of the business. These are examples of real installations across different types of spaces.


Let’s Design Your Security Setup
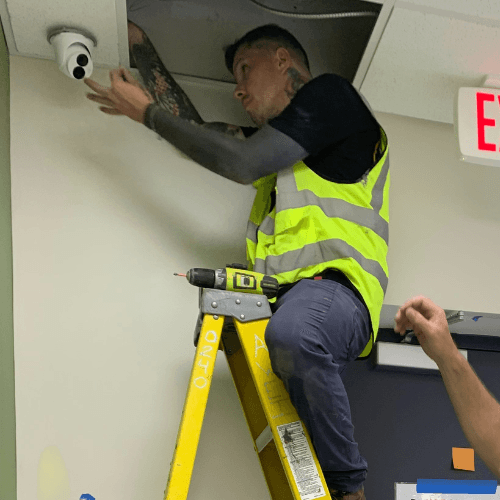
From Planning to Installation
Each installation follows a clear sequence to make sure systems are placed correctly and work as expected. The goal is to avoid gaps, reduce rework, and make sure everything runs reliably from day one.
Site Walkthrough & Planning
Review the space, entry points, and coverage areas to determine camera placement and access control needs.
System Design & Layout
Map out camera positions, access points, and system connections based on how the business operates.
Installation &
Setup
Install cameras, access control hardware, and wiring, then configure the system for proper operation.
Testing &
Handoff
Test coverage, access, and functionality, then walk through the system so everything is clear and ready to use.

Built for Reliability from Start to Finish
Security systems need to be installed correctly and supported over time to be effective. The focus is on doing the work right, keeping systems reliable, and making sure everything continues to function as expected.

After-Hours Installation
Professional Installation Team
End-to-End Ownership
Integrated with White Glove Managed IT
Built To Scale
Ongoing Support
Local Camera & Security Installation Across Central Indiana