Understanding your regulatory obligations starts with knowing what applies to your business. We help clarify requirements and implement the technical controls needed to support ongoing compliance.
- White Glove Managed IT
- Simulated Scenario Testing
- Remote Desktop Server
- Remote Access Configuration
- Virtualization Setup & Maintenance
- Virtual Server Hosting
- Tech365 Cloud Support
- Amazon AWS & Google Cloud
- Tech365 Managed Backup
- Google Apps & Office 365
- Amazon AWS & Google Cloud
- Managed Enterprise DNS
- Tech365 Website Hosting
- Tech365 Hosted Business Phone
- Tech365 Network Monitoring
- Tech365 Managed Backup
- Virus and Spyware Removal
- Virtualization Setup & Maintenance
- Complete Systems Backup
- Disaster Recovery
- Microsoft Azure Setup & Management
- Monday.com Setup, Integration, & Automation
- Periodic Recovery Testing
- Simulated Scenario Testing
- Redundant Backup Infrastructure
- Tech IT Out
- About
- Services
- White Glove Managed IT
- Onsite & Physical IT Support
- Remote, Cloud, & Helpdesk Support
- Simulated Scenario Testing
- Remote Desktop Server
- Remote Access Configuration
- Virtualization Setup & Maintenance
- Virtual Server Hosting
- Tech365 Cloud Support
- Amazon AWS & Google Cloud
- Tech365 Managed Backup
- Google Apps & Office 365
- Amazon AWS & Google Cloud
- Managed Enterprise DNS
- Tech365 Website Hosting
- Tech365 Hosted Business Phone
- Compliance Services
- Business Continuity
- Tech365 Network Monitoring
- Tech365 Managed Backup
- Virus and Spyware Removal
- Virtualization Setup & Maintenance
- Complete Systems Backup
- Disaster Recovery
- Microsoft Azure Setup & Management
- Monday.com Setup, Integration, & Automation
- Periodic Recovery Testing
- Simulated Scenario Testing
- Redundant Backup Infrastructure
- Security Services
- Custom App Development
- Website & Internet Marketing
- Industries
- Tech IT Out
- Let’s Connect
- About
- Services
- White Glove Managed IT
- Onsite & Physical IT Support
- Remote, Cloud, & Helpdesk Support
- Simulated Scenario Testing
- Remote Desktop Server
- Remote Access Configuration
- Virtualization Setup & Maintenance
- Virtual Server Hosting
- Tech365 Cloud Support
- Amazon AWS & Google Cloud
- Tech365 Managed Backup
- Google Apps & Office 365
- Amazon AWS & Google Cloud
- Managed Enterprise DNS
- Tech365 Website Hosting
- Tech365 Hosted Business Phone
- Compliance Services
- Business Continuity
- Tech365 Network Monitoring
- Tech365 Managed Backup
- Virus and Spyware Removal
- Virtualization Setup & Maintenance
- Complete Systems Backup
- Disaster Recovery
- Microsoft Azure Setup & Management
- Monday.com Setup, Integration, & Automation
- Periodic Recovery Testing
- Simulated Scenario Testing
- Redundant Backup Infrastructure
- Security Services
- Custom App Development
- Website & Internet Marketing
- Industries
- Tech IT Out
- Let’s Connect
Prepared For Compliance Regulations

COMPLIANCE SUPPORT
Compliance & Data Protection Services
Compliance at Tech365 is built into how your business operates. We implement practical safeguards and provide ongoing oversight so you stay protected and audit-ready.
Client Expectations
Data Protection Standards
Audit Readiness
Security Safeguards
START WITH A COMPLIMENTARY COMPLIANCE CONSULTATION
Let’s review your requirements, clarify expectations, and outline a practical compliance path for your business.

POSITIVE BUSINESS IMPACT
When Compliance Is Handled Well
Effective compliance creates stability and reduces disruption across the business. With the right controls in place, organizations operate more confidently and avoid unnecessary risk.
The Value Of Strong Compliance

“Tech365 went above and beyond helping us implement the security measures and training required to pass our government audit.Their knowledge, professionalism, and genuine care made a stressful process manageable. We are incredibly thankful for their support when we needed it most.”
Vanessa Hadley
COMPLIANCE SUPPORT OVERVIEW
How We Support Compliance
Compliance is built into how your business operates, not handled as a one-time task. Tech365 provides structured, ongoing support to keep you protected, prepared, and aligned with requirements.
Identify Your Risk
We identify real industry risks so there are no surprises from regulators, insurers, or clients.
Protect What Matters
We put clear, practical safeguards in place that actually fit how your business operates.
Stay Audit Ready
Your documentation and controls are organized, current, and ready when questions or reviews happen.
Compliance That Scales
We stay involved, adjust as requirements change, and keep your compliance aligned as you grow.

PROTECTION FOR YOUR BUSINESS
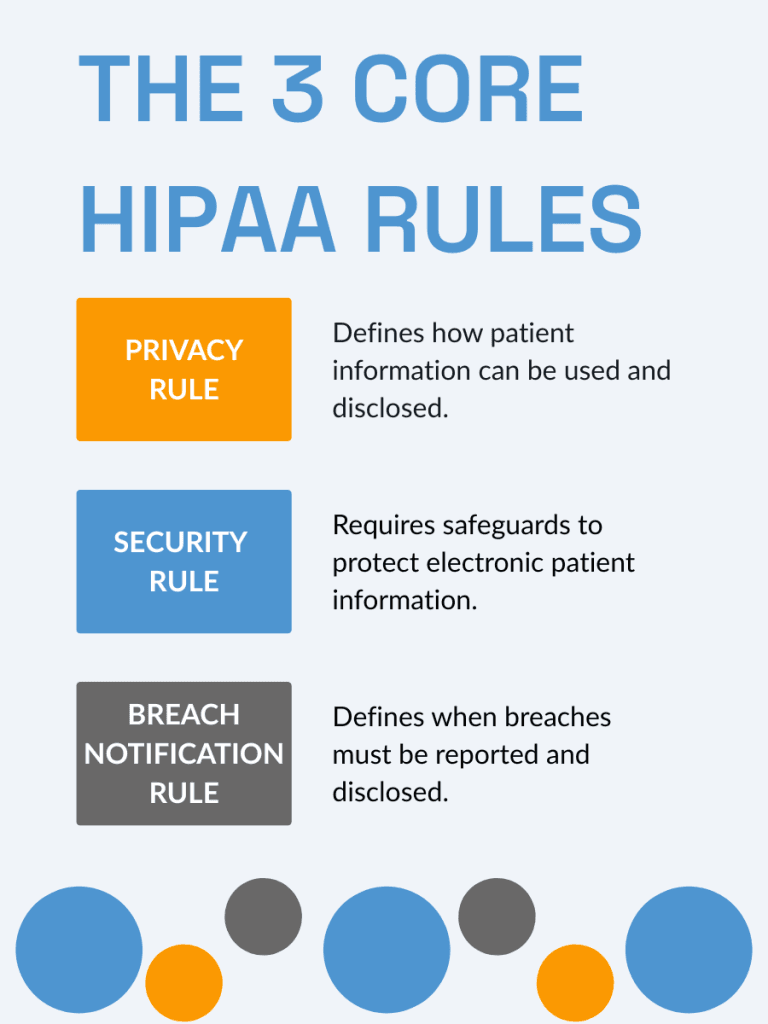
How We Support HIPAA Compliance
HIPAA is more than a checklist. It is about securing your systems, reducing risk, and making sure a breach does not turn into a business crisis.
What We Actually Do
We handle the security controls behind HIPAA so your business is protected, not exposed.

SOC 2 COMPLIANCE
Build Trust With Stronger Security Controls
We implement the technical controls required to meet third party security standards and pass independent audits. From access management to penetration testing, we strengthen your systems and guide you toward compliance.
Controls Auditors Expect
We implement the technical safeguards required for a successful audit without disrupting your operations
Validate & Prove Your Security
We test your environment and document findings so you are prepared for auditor review and customer scrutiny.

ISO 27001 COMPLIANCE
Strengthen Global Credibility With Security Controls
We implement the technical safeguards required to support ISO 27001 certification and formalize your security posture. From access management to continuous monitoring, we help align your infrastructure with internationally recognized standards.

Technical Controls That Support Certification

REGULATORY COMPLIANCE
Align Your Business With Regulatory Standards
How Do I Know Which Regulations Apply To My Business?
Compliance requirements depend on your industry, the type of data you handle, your clients, and where you operate. Many organizations are subject to multiple standards at once.
What If We Are Not Sure Where To Start?
The first step is identifying what regulations and contractual requirements apply to you. A structured review clarifies your obligations and prioritizes next steps.
What Are The Risks Of Non Compliance?
Non compliance can lead to fines, contract loss, reputational damage, and operational disruption. In many cases, it also delays sales cycles and vendor approvals.
Do We Need Formal Certification Or Just Strong Controls?
Some industries require formal certification, while others require documented safeguards and evidence of security practices. The right path depends on your contracts and regulatory environment.
What Is Typically Involved In Becoming Compliant?
Most frameworks require documented policies, technical safeguards, access controls, monitoring, risk management, and ongoing review. Compliance is an ongoing process, not a one time project.
How Long Does Compliance Take?
Timelines vary based on your current security posture and the framework involved. Organizations starting from scratch typically require structured implementation and remediation before certification.
Does Compliance Only Apply To Large Enterprises?
No. Small and mid sized businesses are increasingly required to meet regulatory and security standards, especially when working with larger partners or handling sensitive data.
How Does Tech365 Support Regulatory Compliance?
We implement and manage the technical controls required across common regulatory frameworks. Our role is to strengthen your infrastructure, align your systems with requirements, and support ongoing compliance efforts.
COMPLIANCE SERVICES
Complete Compliance & Security Support
We implement and manage the controls that support regulatory requirements, risk reduction, and continuous oversight. Our services help your organization stay prepared, protected, and audit-ready.
HIPAA COMPLIANCE
Protect patient data and reduce compliance risk with structured security controls aligned to HIPAA requirements.
HIPAA COMPLIANCE
Protect patient data and reduce compliance risk with structured security controls aligned to HIPAA requirements.
SOC 2 READINESS
Demonstrate strong security practices and prepare your organization for independent audit and enterprise scrutiny.
SOC 2 READINESS
Demonstrate strong security practices and prepare your organization for independent audit and enterprise scrutiny.
ISO 27001 COMPLIANCE
Establish a structured information security management system aligned with internationally recognized standards.
ISO 27001 COMPLIANCE
Establish a structured information security management system aligned with internationally recognized standards.
RISK ASSESSMENTS
Understand where your security stands before issues turn into incidents.
RISK ASSESSMENTS
Understand where your security stands before issues turn into incidents.
Tech365 NETWORK MONITORING
Maintain continuous visibility across your environment to detect issues before they disrupt operations.
Tech365 NETWORK MONITORING
Maintain continuous visibility across your environment to detect issues before they disrupt operations.
SECURITY AWARENESS TRAINING
Turn your team into a stronger first line of defense against phishing, fraud, and social engineering.
SECURITY AWARENESS TRAINING
Turn your team into a stronger first line of defense against phishing, fraud, and social engineering.
CYBER INSURANCE & RISK REQUIREMENTS
Meet Today’s Cyber Insurance Security Requirements
Cyber insurance providers now require documented security controls before issuing or renewing coverage. We help ensure your systems align with insurer expectations so you can qualify with confidence.
Multi Factor Authentication
Most insurers require multi factor authentication for email, remote access, and administrative accounts to reduce breach risk.
Endpoint Protection & Monitoring
Advanced endpoint detection and continuous monitoring are often required to identify and respond to threats quickly.
Secure Backups & Recovery
Insurers expect protected, tested backups that can restore operations in the event of ransomware or system failure.
Documented Security Practices
Carriers increasingly require evidence of policies, access controls, and incident response planning during underwriting and renewal.
Multi Factor Authentication
Most insurers require multi factor authentication for email, remote access, and administrative accounts to reduce breach risk.
Endpoint Protection & Monitoring
Advanced endpoint detection and continuous monitoring are often required to identify and respond to threats quickly.
Secure Backups & Recovery
Insurers expect protected, tested backups that can restore operations in the event of ransomware or system failure.
Documented Security Practices
Carriers increasingly require evidence of policies, access controls, and incident response planning during underwriting and renewal.
Multi Factor Authentication
Most insurers require multi factor authentication for email, remote access, and administrative accounts to reduce breach risk.
Endpoint Protection & Monitoring
Advanced endpoint detection and continuous monitoring are often required to identify and respond to threats quickly.
Secure Backups & Recovery
Insurers expect protected, tested backups that can restore operations in the event of ransomware or system failure.
Documented Security Practices
Carriers increasingly require evidence of policies, access controls, and incident response planning during underwriting and renewal.
Multi Factor Authentication
Most insurers require multi factor authentication for email, remote access, and administrative accounts to reduce breach risk.
Device Protection & Monitoring
Advanced endpoint detection and continuous monitoring are often required to identify and respond to threats quickly.
Secure Backups & Recovery
Insurers expect protected, tested backups that can restore operations in the event of ransomware or system failure.
Documented Security Practices
Carriers increasingly require evidence of policies, access controls, and incident response planning during underwriting and renewal.
RELATIONSHIPS OVER INVOICE
What Partnership Means To Tech365
We're There When You Need Us
Onsite, by phone, or remote, we resolve issues & keep your team productive.
We Learn Your Business
We listen first, then tailor support that fits your goals, systems, & growth plans.
We Support Your Whole System
We align tech, security, & strategy so everything runs smoothly together.
We're Here For The Long Haul
We guide your growth & innovation with steady, realiable local IT support.